| 导读 | DenyHosts是用python2.3编写的一个程序,会分析/var/log/secure等文件,当发现同一个ip进行多次ssh登录失败时会将其写入/etc/hosts.dengy文件,达到屏蔽该ip的目的。 |

下载DenyHosts包
[root@localhost ~]# wget //jaist.dl.sourceforge.net/project/denyhosts/denyhosts/2.6/DenyHosts-2.6.tar.gz
安装DenyHosts
[root@localhost ~]# tar xf DenyHosts-2.6.tar.gz [root@localhost ~]# cd DenyHosts-2.6 [root@localhost DenyHosts-2.6]# python setup.py install
制作配置文件
[root@localhost DenyHosts-2.6]# cp denyhosts.cfg-dist /etc/denyhosts.cfg [root@localhost DenyHosts-2.6]# cp daemon-control-dist daemon-control [root@localhost DenyHosts-2.6]# chown root daemon-control [root@localhost DenyHosts-2.6]# chmod 700 daemon-control
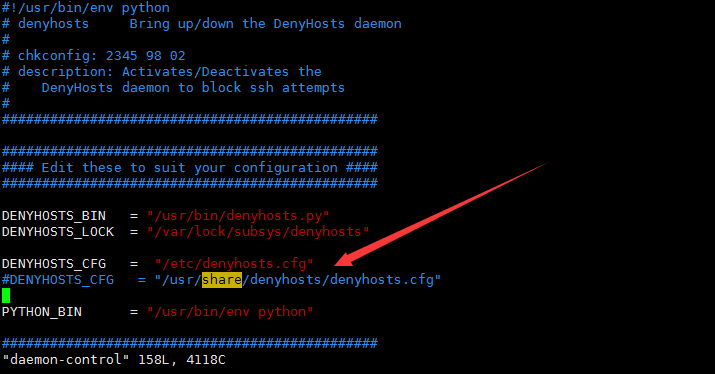
修改配置文件
将daemon-control中的#DENYHOSTS_CFG = "/usr/share/denyhosts/denyhosts.cfg"改为 DENYHOSTS_CFG = "/etc/denyhosts.cfg"
启动
[root@localhost DenyHosts-2.6]# ./daemon-control start(注意相对路径)
测试另外一台服务器远程连接172.16.1.16
默认允许五次,测试发现登陆失败五次之后不允许登陆
[root@localhost ~]# ssh abc@172.16.1.16 abc@172.16.1.16's password: Permission denied, please try again. abc@172.16.1.16's password: Permission denied, please try again. abc@172.16.1.16's password: Permission denied (publickey,gssapi-keyex,gssapi-with-mic,password). [root@localhost ~]# [root@localhost ~]# ssh abc@172.16.1.16 abc@172.16.1.16's password: Permission denied, please try again. abc@172.16.1.16's password: Permission denied, please try again. abc@172.16.1.16's password: Permission denied (publickey,gssapi-keyex,gssapi-with-mic,password). [root@localhost ~]# ssh abc@172.16.1.16 abc@172.16.1.16's password: Permission denied, please try again. abc@172.16.1.16's password: Permission denied, please try again. abc@172.16.1.16's password: Permission denied (publickey,gssapi-keyex,gssapi-with-mic,password). [root@localhost ~]# ssh abc@172.16.1.16 abc@172.16.1.16's password: Permission denied, please try again. abc@172.16.1.16's password: Permission denied, please try again. abc@172.16.1.16's password: Permission denied (publickey,gssapi-keyex,gssapi-with-mic,password). [root@localhost ~]# ssh abc@172.16.1.16 ssh_exchange_identification: read: Connection reset by peer
查看hosts.deny文件
登陆连续失败之后就会把ip地址写在hosts.deny文件
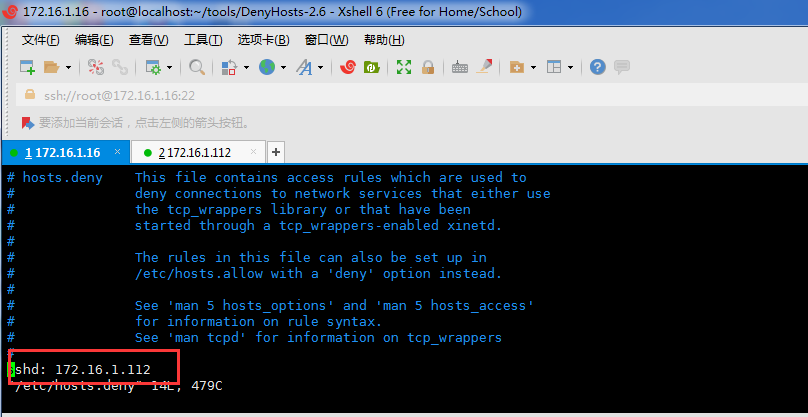
172.16.1.112的ip已经被限制,到此功能实现。
本文原创地址://q13zd.cn/centos-denyhosts.html编辑:王华超,审核员:逄增宝